Wazzup Pilipinas!
Enterprises have rapidly incorporated cloud computing over the last decade, and that trend only seems to be accelerating. Private cloud infrastructure, including virtualization and software-defined networking (SDN), is in the process of transforming on-premise data centers, which host the majority of enterprise server workloads around the world. Enterprises are also embracing public clouds at an unprecedented rate, with most connecting back to on-premise environments to create a true hybrid cloud environment. For all their advantages, these accelerated infrastructural changes also raise major concerns about security, and the ability to protect end-users and sensitive data from ever-evolving cyber threats.
As today’s enterprise data centers evolve from static internal environments to a mix of private, public, and hybrid clouds, organizations need to augment traditional firewalls and security appliances (deployed for north-south traffic at the network edge) with expanded protection for east-west traffic moving laterally across the network, both within internal networks and across clouds.
To maintain a strong security posture in private, public, and hybrid clouds, organizations need to increase and perhaps even reallocate security to keep pace with these more dynamic, distributed, and fast-paced environments.
Here are some specific areas to consider:
Scalability
Cloud computing enables the rapid development and delivery of highly scalable applications. Security needs to be equally elastic to scale with the cloud infrastructure itself and to provide transparent protection without slowing down the business.
Today’s cloud environments require ultra-fast physical firewalls that provide highly scalable north-south data center firewall and network security protection at the edge of the private cloud. They also need virtual firewalls that provide north-south protection for public clouds. And they need virtual firewalls that provide east-west protection for data and transactions moving between devices in the cloud. High-performance firewalls and network security appliances need to scale vertically to meet volume and performance demands, and laterally to seamlessly track and secure data from IoT/endpoints, across the distributed network/data center, and into the cloud.
Segmentation
With the IT efficiencies gained by pooling resources (e.g., compute, storage, network) through technologies such as virtualization and software-defined networking (SDN), cloud environments have become increasingly aggregated to the point where entire data centers can be consolidated. If a hacker or advanced threat breaches the cloud perimeter via a single vulnerable application, there’s typically little to protect critical assets within the flat and open internal network. To minimize that serious potential for damage and loss, organizations need to isolate business units and applications. Networks need to be intelligently segmented into functional security zones to control east-west traffic.
End-to-end segmentation provides deep visibility into traffic that moves east-west across the distributed network, limits the spread of malware, and allows for the identification and quarantining of infected devices. A robust end-to-end segmentation strategy includes internal segmentation firewalling across data centers, campuses, and branch offices, and secure microsegmentation for SDN and cloud environments.
Awareness
In addition to scalability and segmentation, your underlying security infrastructure should offer automatic awareness of dynamic changes in the cloud environment to provide seamless protection. It’s not enough to detect bad traffic or block malware using discrete security devices. Security should be integrated into a SIEM and other analytic tools in private and public clouds that have the ability to collect and correlate data and automatically orchestrate changes to security policy/posture in response to detected incidents and events. The individual elements need to work together as an integrated and synchronized security system with true visibility and control.
Extensibility
Solutions should also be built on an extensible platform with programmatic APIs (for example, REST and JSON) and other interfaces to dynamically integrate with the wide array of deployed hypervisors, SDN controllers, cloud management consoles, orchestration tools, and software-defined data centers and clouds. This enables security that can automatically adapt to the evolving network architecture and changing threat landscape.
Choosing a cloud security solution
When evaluating a security solution, there are a few general questions that organizations ought to start with.
Is it scalable? A comprehensive security strategy must be elastic in both depth (performance and deep inspection) and breadth (end-to-end).
Is it aware? You need to not only track how data flows in and out of your network, but also how it moves within the perimeter and who has access to it.
Is it really secure? The different tools that protect your network need to work together as an integrated system to provide unified visibility and control.
Is it actionable? You need a common set of threat intelligence combined with centralized orchestration that enables security to dynamically adapt as new threats are discovered and automatically deliver a synchronized response anywhere across the distributed network.
How open is it? Well-defined, open APIs allow technology partners to become part of the fabric — helping to maximize investments while dynamically adapting to changes.
Other specific features to look for might include:
Software-defined Security: Look for a unified security platform with a single OS to enable orchestration and automation across physical, virtual, and cloud-based security.
Integration: Solutions should integrate with VMware vSphere and NSX environments, as well as public cloud environments like AWS and Azure to provide on-demand provisioning, pay-as-you-go pricing, elastic auto-scaling, and unified analytics that enhance protection and visibility.
Single-Pane-of-Glass Visibility and Control: Your security solution should include centralized management with a consolidated view of policies and events—regardless of physical, virtual, or cloud infrastructure.
Conclusion
The evolving enterprise network combined with the transition to a digital business model present some of the biggest challenges currently facing traditional network security. At the same time, the rapid adoption of private, public, and hybrid clouds is driving the evolution of cloud security.
The next generation of agile and elastic security solutions must transcend the static nature of their forebears to fundamentally scale protection while providing segmentation within and across cloud environments—helping organizations embrace the benefits of an evolving infrastructure while anticipating the attack vectors of current and emerging threats.
Scalability
Cloud computing enables the rapid development and delivery of highly scalable applications. Security needs to be equally elastic to scale with the cloud infrastructure itself and to provide transparent protection without slowing down the business.
Today’s cloud environments require ultra-fast physical firewalls that provide highly scalable north-south data center firewall and network security protection at the edge of the private cloud. They also need virtual firewalls that provide north-south protection for public clouds. And they need virtual firewalls that provide east-west protection for data and transactions moving between devices in the cloud. High-performance firewalls and network security appliances need to scale vertically to meet volume and performance demands, and laterally to seamlessly track and secure data from IoT/endpoints, across the distributed network/data center, and into the cloud.
Segmentation
With the IT efficiencies gained by pooling resources (e.g., compute, storage, network) through technologies such as virtualization and software-defined networking (SDN), cloud environments have become increasingly aggregated to the point where entire data centers can be consolidated. If a hacker or advanced threat breaches the cloud perimeter via a single vulnerable application, there’s typically little to protect critical assets within the flat and open internal network. To minimize that serious potential for damage and loss, organizations need to isolate business units and applications. Networks need to be intelligently segmented into functional security zones to control east-west traffic.
End-to-end segmentation provides deep visibility into traffic that moves east-west across the distributed network, limits the spread of malware, and allows for the identification and quarantining of infected devices. A robust end-to-end segmentation strategy includes internal segmentation firewalling across data centers, campuses, and branch offices, and secure microsegmentation for SDN and cloud environments.
Awareness
In addition to scalability and segmentation, your underlying security infrastructure should offer automatic awareness of dynamic changes in the cloud environment to provide seamless protection. It’s not enough to detect bad traffic or block malware using discrete security devices. Security should be integrated into a SIEM and other analytic tools in private and public clouds that have the ability to collect and correlate data and automatically orchestrate changes to security policy/posture in response to detected incidents and events. The individual elements need to work together as an integrated and synchronized security system with true visibility and control.
Extensibility
Solutions should also be built on an extensible platform with programmatic APIs (for example, REST and JSON) and other interfaces to dynamically integrate with the wide array of deployed hypervisors, SDN controllers, cloud management consoles, orchestration tools, and software-defined data centers and clouds. This enables security that can automatically adapt to the evolving network architecture and changing threat landscape.
Choosing a cloud security solution
When evaluating a security solution, there are a few general questions that organizations ought to start with.
Is it scalable? A comprehensive security strategy must be elastic in both depth (performance and deep inspection) and breadth (end-to-end).
Is it aware? You need to not only track how data flows in and out of your network, but also how it moves within the perimeter and who has access to it.
Is it really secure? The different tools that protect your network need to work together as an integrated system to provide unified visibility and control.
Is it actionable? You need a common set of threat intelligence combined with centralized orchestration that enables security to dynamically adapt as new threats are discovered and automatically deliver a synchronized response anywhere across the distributed network.
How open is it? Well-defined, open APIs allow technology partners to become part of the fabric — helping to maximize investments while dynamically adapting to changes.
Other specific features to look for might include:
Software-defined Security: Look for a unified security platform with a single OS to enable orchestration and automation across physical, virtual, and cloud-based security.
Integration: Solutions should integrate with VMware vSphere and NSX environments, as well as public cloud environments like AWS and Azure to provide on-demand provisioning, pay-as-you-go pricing, elastic auto-scaling, and unified analytics that enhance protection and visibility.
Single-Pane-of-Glass Visibility and Control: Your security solution should include centralized management with a consolidated view of policies and events—regardless of physical, virtual, or cloud infrastructure.
Conclusion
The evolving enterprise network combined with the transition to a digital business model present some of the biggest challenges currently facing traditional network security. At the same time, the rapid adoption of private, public, and hybrid clouds is driving the evolution of cloud security.
The next generation of agile and elastic security solutions must transcend the static nature of their forebears to fundamentally scale protection while providing segmentation within and across cloud environments—helping organizations embrace the benefits of an evolving infrastructure while anticipating the attack vectors of current and emerging threats.
Written by Bill McGee, Director of Communications of Fortinet














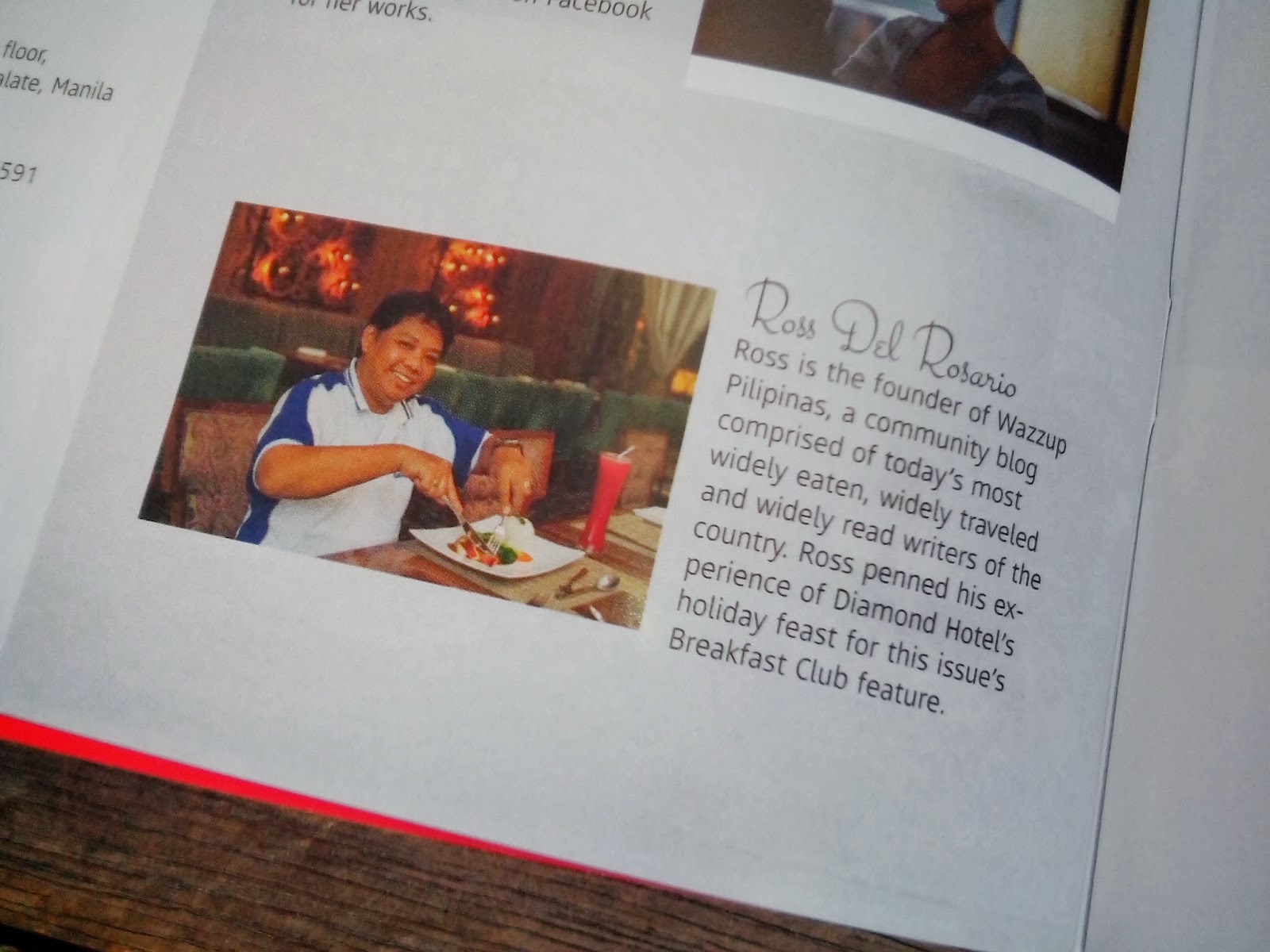
 Ross is known as the Pambansang Blogger ng Pilipinas - An Information and Communication Technology (ICT) Professional by profession and a Social Media Evangelist by heart.
Ross is known as the Pambansang Blogger ng Pilipinas - An Information and Communication Technology (ICT) Professional by profession and a Social Media Evangelist by heart.





hello!! Very interesting discussion glad that I came across such informative post. Keep up the good work friend. Glad to be part of your net community. vpn reviews
ReplyDeletei love reading this article so beautiful!!great job! vpn services
ReplyDelete