Wazzup Pilipinas!
User-based devices that communicate, consume content, and create and publish content for other people to consume have dominated our current version of the Internet. The developing Internet of Things is about to change that. While it will include the “old” Internet of user-based devices, it is very different for one simple reason: billions of new devices connected and tracked at the periphery of the network will not be operated by people. These devices may be semi- or even fully automated, and they will vastly outnumber the human-operated devices in a short period of time.
Like the old Internet, this Internet of Things (IoT) will continue to include data, voice, and video. But it will also contain new assets that will take the Internet from being a network of human-operated devices to a network containing many nonhuman-operated devices—the “things” of IoT.
The IoT contains a variety of technical systems and devices that go by different names, but all fall under the broader IoT umbrella because these systems all share common technology, and often common infrastructure. It’s helpful to review the terminology being used in order to better understand the relationship between these tools and the IoT.
Machine to Machine Communication (M2M)
Machine-to-machine (M2M) systems are part of the IoT, and M2M, like many of the terms to follow, can be seen as a catchall term. The current generation of M2M applications includes both fully automated and semi-automated systems. For example, some of today’s most commonly labeled M2M systems include point-of-sale (POS) and automated vehicle location (AVL) services. POS devices are semi-automated, in that people must initiate and authorize the transactions (ideally), while AVL is an automated system for reporting the geospatial coordinates of assets like trucks and delivery vehicles.
One notable characteristic of current M2M systems is that they are largely unidirectional in data flow or service requests. POS devices, for example, initiate a transaction with central transaction processing systems, but are usually not equipped or intended to support incoming commands. The advantage of the unidirectional nature of these early M2M systems is that exploitation opportunities are more limited: physical access to the remote endpoints is required, while network-based attacks are lower in probability.
Connected Devices
Connected devices is also a catchall term for things other than servers and PCs that are entering the network. Like M2M, they can be automated or semi-automated, but connected devices are more likely to communicate with each other bidrectionally, rather than transmitting but not receiving.
Connected devices tend to envision both a centralized management infrastructure and/or a situation where devices communicate on a peer-to-peer basis, without ever referencing back to any centralized system or server. This peer-to-peer communication offers big advantages in terms of speed of decision-making and reduced loads on networks, but limits potential for oversight and safety controls.
Smart-Everything
From smart appliances to smart houses to smart cities, so much of our world now is intelligent and interconnected, thanks to the IoT. Smart cities, for example, envision using IoT technology to improve the efficiency of services, from transportation systems to hospitals to energy and water supply. These systems will use unimagined combinations of peer-to-peer and client-server based decision-making, ubiquitous networking, and massive amounts of high-assurance bandwidth to move all this data back and forth.
Perhaps the distinguishing feature of the “smart” discussion versus M2M and connected devices is that it tends to be more conceptual and less technical in nature. “Smart” is part of the IoT and will evolve as a notion, with small smart systems joining other small smart systems to create larger smart systems.
Ubiquitous Computing
Ubiquitous Computing (UC) is the most abstract and conceptual term synonymous with the IoT. Devices and systems that use UC are completely connected, and constantly available. In order to realize this pervasive, ubiquitous computing paradigm, a wide range of technologies must be combined, such as industrial sensor networks, multi-medium networking, RFID, M2M, mobile computing, human-computer interaction, and wearable computers.
Though the UC concept involves a variety of technologies, the essence of UC involves the intelligence about, and knowledge of, our surroundings (also referred to as context awareness). By knowing their surroundings, including the dynamic geospatial relationships involving human users and their tools (cars, elevators, medical devices, and even each other), UC systems can offer useful customized services that drive increased personal and business efficiency.
Written By:
Tyson Macaulay, Chief Security Strategist and Vice President of Security Services at Fortinet
https://blog.fortinet.com/2016/07/28/riot-control-what-are-the-things-in-the-iot















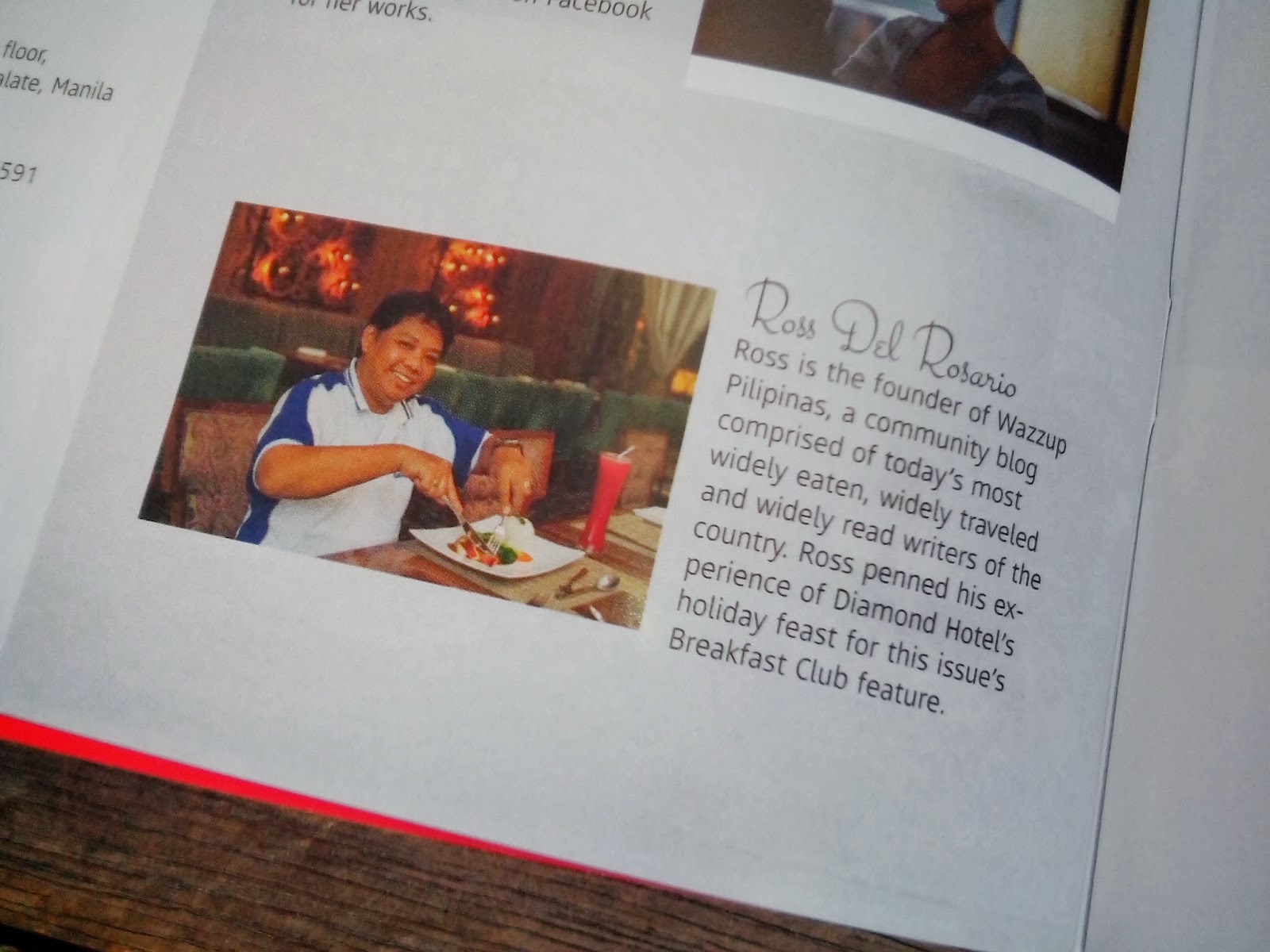
 Ross is known as the Pambansang Blogger ng Pilipinas - An Information and Communication Technology (ICT) Professional by profession and a Social Media Evangelist by heart.
Ross is known as the Pambansang Blogger ng Pilipinas - An Information and Communication Technology (ICT) Professional by profession and a Social Media Evangelist by heart.





Post a Comment